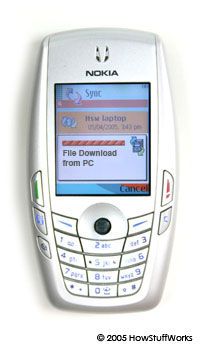
A cell-phone virus is basically the same thing as a computer virus -- an unwanted executable file that "infects" a device and then copies itself to other devices. But whereas a computer virus or worm spreads through e-mail attachments and Internet downloads, a cell-phone virus or worm spreads via Internet downloads, MMS (multimedia messaging service) attachments and Bluetooth transfers. The most common type of cell-phone infection right now occurs when a cell phone downloads an infected file from a PC or the Internet, but phone-to-phone viruses are on the rise.
Current phone-to-phone viruses almost exclusively infect phones running the Symbian operating system. The large number of proprietary operating systems in the cell-phone world is one of the obstacles to mass infection. Cell-phone-virus writers have no Windows-level marketshare to target, so any virus will only affect a small percentage of phones.
Infected files usually show up disguised as applications like games, security patches, add-on functionalities and, of course, pornography and free stuff. Infected text messages sometimes steal the subject line from a message you've received from a friend, which of course increases the likelihood of your opening it -- but opening the message isn't enough to get infected. You have to choose to open the message attachment and agree to install the program, which is another obstacle to mass infection: To date, no reported phone-to-phone virus auto-installs. The installation obstacles and the methods of spreading limit the amount of damage the current generation of cell-phone virus can do.