In 1997, Ford Motor Co. equipped the Mustang with one of the first RFID ignition immobilizers in the U.S. car industry. Theft levels for the Mustang immediately dropped 70 percent from just two years prior [source: Stone]. The results were stunning, and pretty much every other carmaker followed suit.
Today, the RFID (radio frequency identification) industry claims a 90 percent reduction in theft rates for car models equipped with RFID starters, immobilizers and entry systems [source: Vamosi]. Both automakers and insurance companies have full faith in the devices, even going so far as to label them unbeatable. And certainly, the technology is an impressive display of security innovation.
Advertisement
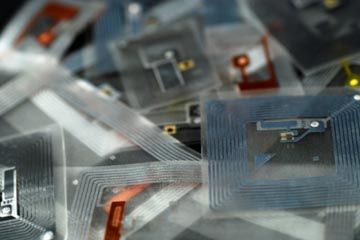
RFID relies on radio-frequency signals to create a system that, for the first several years it was in use, was indeed uncrackable. In the 1990s, many a car thief was thwarted by the rather brilliant addition of RFID immobilizers to regular old physical keys. An RFID immobilizer is a chip embedded in the top part of an ignition key. This chip sends out an encrypted string of radio-frequency signals, basically a particular number of impulses broadcast on various radio frequencies to create a specific code, when the driver inserts it into the ignition-key slot. Without this code, the car either won't start or won't activate the fuel pump. So even if someone hotwires the car or copies an ignition key, the ignition isn't going to work because it hasn't received the proper radio-frequency code.
If you have a car that comes with a special "valet key," the immobilizer probably shuts down the fuel pump if the car is started without the code. This means the car is going to run only on whatever fuel is left in the fuel line, which will only get it a couple of blocks. Thus the valet key -- valet parkers only have to drive a car very short distances. If they try to drive off with your car, they won't get very far. Neither will any other potential car thief.
Early RFID systems, both keyless entry (the key fob device with the button you press to unlock the car) and vehicle immobilizers, used 32-bit encryption. That means they sent a code of 32 impulses. With 32 bits in the code, there are billions of possible combinations [source: Stone]. In newer schemes, including remote starters that let you start a car with the push of a button, the codes have 40 bits, which increases the possibilities. With so many possible codes, the system seems unbeatable.
And at first, it was.
In this article, we'll see whether RFID technology can protect a car from theft and find out how thieves are adapting to the systems. We'll also look at some tips to help you further secure an RFID-protected car.
But first, let's see how the system operates.
Advertisement