Your computer could be committing crimes right now. Even as you read this article, it could be working as part of a secret network of machines designed to bring down Web sites or flood e-mail boxes with ads for low mortgages or erectile dysfunction medications. If the authorities link attacks back to your computer, you might take the fall even though you're not at fault.
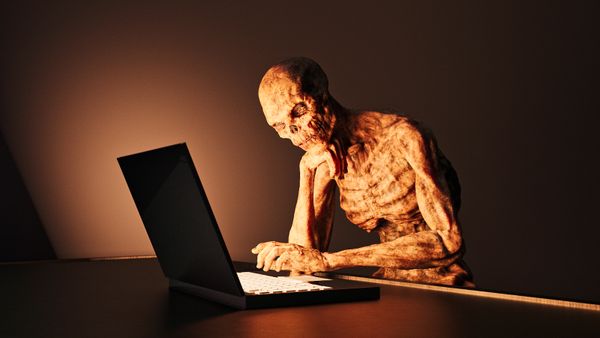
Whether you call it a zombie computer army or a botnet, it's bad business -- millions of computers have already fallen under the control of malicious hackers known as crackers. These crackers rely on several strategies aimed at getting you to download and execute a piece of malicious software, or malware. If you fall into the trap, your computer becomes compromised.
Advertisement
What can happen if your computer becomes a zombie? Zombie applications give crackers access to your machine, usually by exploiting a security vulnerability or creating a backdoor entry point. Once a cracker establishes this link, he or she can manipulate your computer. Some botnet applications allow the cracker to control your computer remotely. Others give the cracker the ability to look at your private information and steal your identity.
One of the most common botnet applications is spam distribution. According to Symantec's MessageLabs, the Cutwail botnet alone was responsible for 6.5 percent of all spam messages in February 2009 [source: MessageLabs]. That means the computers of innocent victims are sending out millions of e-mail messages to people around the world.
Another botnet application is the distributed denial of service (DDoS) attack. The cracker first creates a large botnet by convincing victims to execute malware. Then the cracker arranges an attack on a particular Web server at a specific time. When that time comes, the botnet computers simultaneously send messages to the target Web server. The sudden rush of Internet traffic makes the Web server unstable and brings it down. The victims of these attacks are often high profile targets like CNN and Yahoo.
So what do you do if you discover your computer is part of a botnet?
Advertisement